I just added VRM Hub Blog to the ‘roll on the right. Lots going on there, as in the Hub itself. Of special note are Ownership of data, privacy policies and other VRM creatures and Whose data is it anyway? In those Adriana unpacks some of what she’s slso been posting to the ProjectVRM list. Adriana also posts her own notes from the latest meeting.
Jay Deragon asks, Does Disequilibrium Precede Disruption?
In Venn and the Art of Data Sharing, Eve Maler presents this useful graphic:
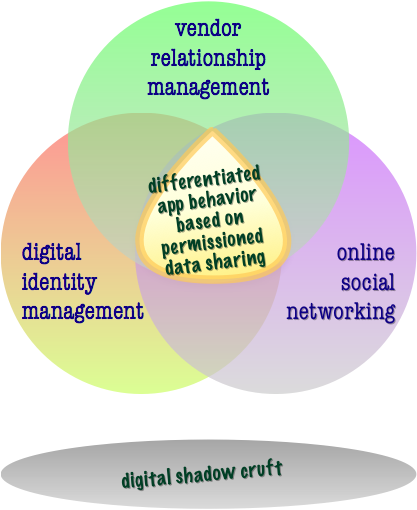
She explains,
VRM partly involves what could be called restriction of data flow — undoing vendors’ grip on users’ info in a way that’s familiar to proponents of privacy-enhanced and user-controlled IdM. But other VRM scenarios involve enhancement of individuals’ opportunities to share personal information, for example by issuing a personal RFP to potential vendors. As Doc Searls has said, VRM is “personal first and social second”, so it seems to have a closer kinship with digital identity but could provide new social opportunities as well.
Eve does a good job describing how VRM can get social while not subordinating to social networking, its scenarios or its technologies. The same goes for VRM and identity. This last point is especially significant in respect to a pair of upcoming identity events: next week’s Digital ID World (DIDW), and the  Internet Identity Workshop (IIW2008b) coming up on November 10-12 (and about which Phil Windley says more here). VRM can contribute to identity conversation and tech development — and even be part of that work — without being a subset of that work. I’ll be talking more about this in my keynote at DIDW this coming week.
Internet Identity Workshop (IIW2008b) coming up on November 10-12 (and about which Phil Windley says more here). VRM can contribute to identity conversation and tech development — and even be part of that work — without being a subset of that work. I’ll be talking more about this in my keynote at DIDW this coming week.
By the way, mark your calendars for the next VRM Workshop (VRM2008b), scheduled for the day after IIW in the Bay Area. The location is not yet determined. (If you have any good ideas, suggest them.)

0 Comments
2 Pingbacks